Google Chrome will warn users on non-secure websites by 2017

Chrome Security Team member Emily Schechter disclosed the news through a post on Google’s Online Security Blog. From then on, Chrome will indicate connection security with an icon in the address bar to help users browse the web safely.
Historically, Chrome didn’t explicitly warn users about HTTP connections, but the Chrome 56 browser version will start marking HTTP sites that deal with passwords or credit cards as non-secure. Eventually, Google intends to flag all HTTP sites as such.
Chrome currently shows HTTP connections with a neutral indicator that doesn’t reflect the real security dangers for HTTP connections. When users load a website over HTTP, someone else on the network can look at the site, and even modify it, before it gets to them.
Google wants sites to go from HTTP to HTTPS
The transition from HTTP to HTTPS is constantly increasing, and Google seeks to accelerate that movement with its new security plan. One way to establish an encrypted HTTP connection, and therefore make it more secure, is HTTP Secure (HTTPS).
At the moment, more than half of Chrome desktop page loads are now serving over HTTPS, and since Google released its HTTPS report on February, 12 of the top 100 websites changed their serving default from HTTP to HTTPS.
Google’s plan to label HTTP sites as non-secure in a more precise and accurate way will happen by steps. Chrome 56 will deal with HTTP pages that handle password or credit card details, and subsequent releases will label all sites as non-secure regardless of their nature.
The tech giant vowed to publish updates about the matter and insisted pages shouldn’t wait to move to HTTPS. According to Google, HTTPS is now easier and cheaper and offers better performance as well as new features that HTTP can’t handle.
About Google Chrome’s security
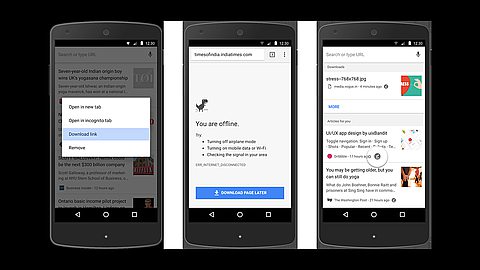
Now and then Chrome retrieves updates of phishing and malware blacklists to warn users when they visit potentially harmful sites. Google has download scanning protection since Chrome 17 and features the Incognito mode for private browsing.
Between 2009 and 2011, no security vulnerabilities in Chrome got exploited in the annual computer hacking contest Pwn2Own. However, at the 2012 edition, a French hacker team overcame Chrome’s sandboxing. Google made fixes for the vulnerabilities within 10 hours of the submission.